Keylogger
Purpose
For my project, I created a basic keylogger designed for educational and cybersecurity research purposes. The primary goal was to understand how malware operates at a low level, how attackers capture user input, and—most importantly—how to defend against these threats. Building the tool gave me hands-on experience with system events, keyboard hooks, and secure logging practices. I made sure to run and test it only in a controlled environment, such as a virtual machine, since keylogging technology can be harmful if misused.
how it was built
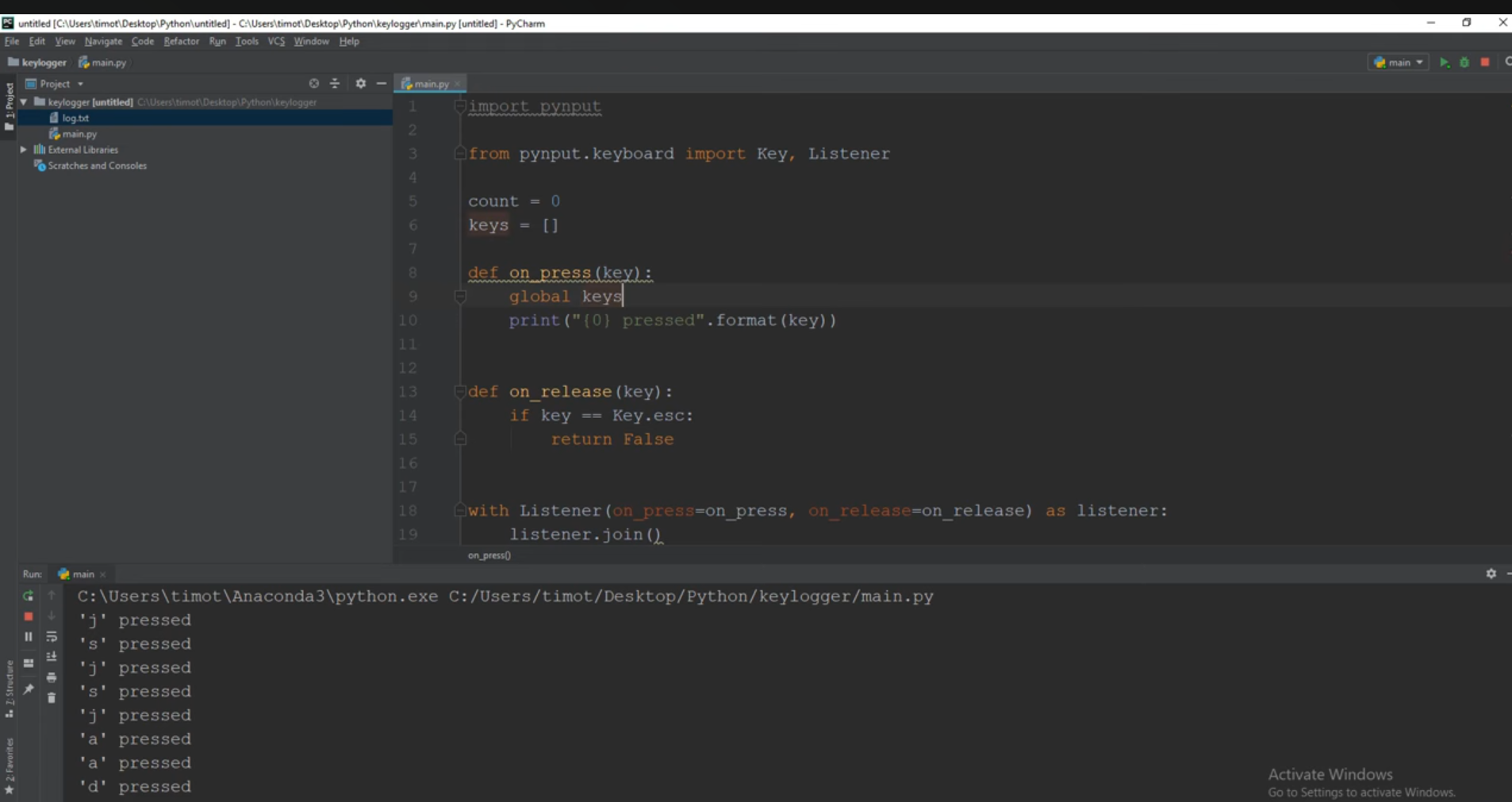
To build the keylogger, I coded it in python and implemented a keyboard hook that intercepts keypress events at the operating system level. The program runs in the background and records every keystroke, storing the output in a secure local file so I could analyze how the captured data looks. I also added features like timestamping, basic formatting to convert key codes to readable characters, and safeguards so the logger stops automatically after testing. Throughout development, I focused on understanding concepts such as event listeners, file handling, and how antivirus software detects suspicious behavior.
Importance
Another important part of the project was learning about the ethical and legal responsibilities that come with creating tools like this. Keyloggers are often used maliciously, so studying them helps security professionals identify indicators of compromise and build defenses. By creating my own simple version, I was able to see firsthand how stealthy these programs can be, what patterns they leave in system logs, and how endpoint protection tools respond. This knowledge is valuable for cybersecurity work, where defending users and systems depends on understanding how attackers think.
Summary
Overall, the project helped me develop both technical skills and practical security awareness. I learned how keyloggers function, how to design and test one safely, and how important it is to apply cybersecurity tools responsibly. The experience gave me a deeper appreciation of how critical it is to combine technical ability with ethical decision-making, especially in fields like cybersecurity and networking.
